In the ever-evolving landscape of cybersecurity, the emergence of sophisticated threats is a constant challenge. One such alarming development is the XMRig campaign, which has recently gained attention for its cunning use of social engineering and innovative techniques to seize control of unsuspecting systems. According to Trellix, this campaign employs pirated software bundles to lure users into deploying a customized XMRig miner, highlighting the need for enhanced vigilance and protective measures in today’s digital environment. With the potential to destabilize victim systems and a growing prevalence of cryptojacking attacks, understanding the intricacies of the XMRig campaign is crucial for individuals and organizations alike.
Understanding the Mechanics of the XMRig Campaign
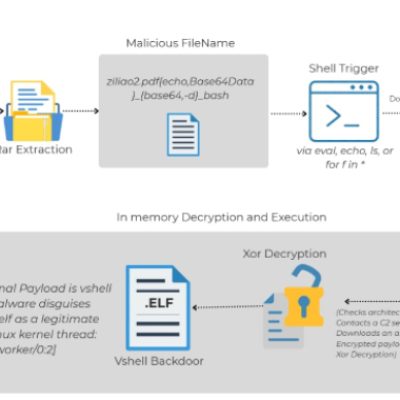
The XMRig campaign exemplifies a multi-faceted approach to cryptojacking, deeply leveraging social engineering tactics. By masquerading as free premium software, attackers entice users to unwittingly download malicious executables embedded in pirated software bundles, such as office productivity suite installers. The payload, often referred to as a “dropper,” serves multiple roles, functioning as an installer, watchdog, and manager for various aspects of the attack lifecycle.
The research conducted by Trellix reveals that the malware system is modular, maintaining a flexible design that distinguishes its core functionalities, including cryptocurrency mining and privilege escalation. This adaptability allows for sophisticated operations, often leveraging command-line arguments to switch modes seamlessly during installation. For example:
- No parameter—validates the environment and facilitates migration.
- 002 Re:0—drops main payloads, initiates mining, and enters a monitoring phase.
- 016—restarts the miner if terminated.
- barusu—executes a self-destruct sequence to eliminate all traces of the malware.
Another noteworthy feature of this campaign is its use of a time-based logic bomb that governs its actions. The malware continually checks the local system time against a predetermined date, leading to strategic behavior adjustments depending on the current timeline. If the date is before December 23, 2025, the campaign continues its operations; after this date, it initiates a self-destruct sequence.
Propagating Threats: How the XMRig Campaign Spreads
A critical aspect of the XMRig campaign is its worm-like capabilities, enabling it to propagate effectively. Unlike traditional malware that depends solely on user action to spread, this variant of XMRig actively seeks out opportunities to replicate itself across networks via external storage devices. This aggressive dissemination strategy transforms it from a mere Trojan horse into a formidable worm capable of infiltrating multiple systems.
Crucially, the XMRig campaign integrates a vulnerability known as CVE-2020-14979 into its operations, utilizing a flawed driver (WinRing0x64.sys) to gain elevated privileges. This technique, known as BYOVD (Bring Your Own Vulnerable Driver), significantly boosts the mining performance by enhancing the RandomX hashrate by an estimated 15% to 50%. The careful orchestration of social engineering, legitimate software disguise, and kernel-level exploitation underscores the resilience and efficiency of this cryptojacking campaign.
For a deeper understanding of how vulnerabilities are exploited in similar scenarios, check out our analysis on exploitation timelines.
Recent Activity and Impact of the XMRig Campaign
Evidence indicates that mining activities associated with the XMRig campaign began to manifest sporadically in November 2025, culminating in a spike of activity on December 8, 2025. This uptick highlights the campaign’s operational effectiveness and the seriousness of cryptojacking as a cybersecurity threat. By intertwining advanced technologies with traditional exploits and social engineering techniques, the attackers have established a durable and efficient botnet that opens doors for unauthorized use of computational resources.
Additionally, the impact of this campaign extends beyond mere financial loss for victims. As highlighted in other cybersecurity insights, similar campaigns continue to exploit gaps in defense mechanisms, as explored in our analysis of cybersecurity strategies for 2025.
Mitigating Risks and Enhancing Security Posture
As the XMRig campaign serves as a cautionary tale, organizations must remain proactive in fortifying their defenses against such evolving threats. Key strategies include:
- Education and awareness—Training employees about the dangers of downloading pirated software and recognizing social engineering tactics.
- Regularly updating software—Implementing security patches to close vulnerabilities that may be exploited by attackers.
- Use of proper cybersecurity tools—Integrating advanced malware detection systems and employing endpoint protection solutions.
By adopting these measures, businesses can significantly diminish their risk exposure, particularly concerning sophisticated attackers who employ tactics similar to those observed in the XMRig campaign.
For additional insights into the exploitation of vulnerabilities, consider reviewing our report on the WhatsApp Worm, which outlines similar attack strategies and preventive measures.
Conclusion: Staying Ahead of Cyber Threats
The XMRig campaign exemplifies the significant challenges that organizations face in the current cybersecurity landscape. By combining social engineering with innovative malware techniques, this campaign illustrates the growing sophistication of cybercriminals. Educating users, maintaining vigilant cybersecurity practices, and being aware of the latest threats are essential steps toward achieving greater resilience against such attacks.
To deepen this topic, check our detailed analyses on Cybersecurity section.