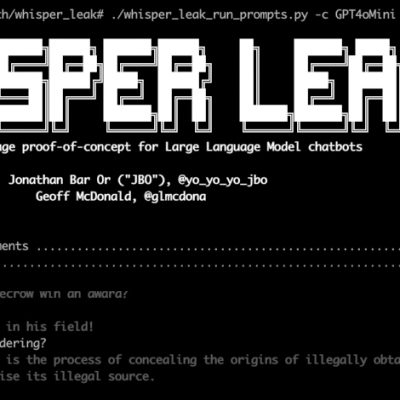
With the rapid evolution of digital threats, understanding how to safeguard systems has never been more crucial. One of the latest challenges in cybersecurity is the emergence of the SesameOp backdoor, a sophisticated malicious tool detected by Microsoft that utilizes OpenAI’s API as a stealth command channel. This form of cyberattack not only exemplifies the dangers lurking in our digital world but also emphasizes the importance of robust security measures. In this article, we will explore the nuances of the SesameOp backdoor, its implications on cybersecurity, and how organizations can prepare to better defend themselves against such threats.
Understanding the Risks: What is the SesameOp Backdoor?
The SesameOp backdoor is not just another piece of malware; it represents a growing trend where cybercriminals leverage artificial intelligence to enhance their attacks. This tool has been reported to communicate through OpenAI’s API, allowing it to operate under the radar and effectively evade traditional security measures. By disguising its activities, the SesameOp backdoor makes it significantly challenging for security teams to detect and neutralize potential threats.
Recent reports highlight that tools like SesameOp backdoor are designed to exploit vulnerabilities within common software applications. For example, these tools often utilize phishing techniques to gain access to sensitive systems, making awareness and training crucial for all employees. Take action now by investing in security awareness programs that educate users about these dangerous tactics.
How Organizations Can Combat the SesameOp Threat
Defending against the SesameOp backdoor requires a multifaceted approach. Organizations must adopt a layered security strategy that encompasses effective detection, prevention, and response mechanisms. Here are several effective strategies:
- Invest in Advanced Threat Detection: Utilize security tools that leverage machine learning and AI to identify anomalies that suggest a breach.
- Regularly Update Software: Ensure all applications are kept up to date to mitigate vulnerabilities that the SesameOp backdoor may exploit.
- Implement Strong Access Controls: Limit access to sensitive information and systems to only those who require it, thereby reducing potential entry points for attackers.
Additionally, having an incident response plan in place can significantly minimize damage in the event of a breach. As examined in our analysis of cybersecurity policy reform, a proactive approach is critical to maintaining security integrity in today’s threat landscape.
Monitor Cautiously: The Role of Continuous Vigilance
Adopting a mindset of continuous vigilance is paramount in countering the SesameOp backdoor. Regular monitoring of network activity can help identify unusual behavior before it escalates into a larger issue. Employing security information and event management (SIEM) systems allows organizations to gather and analyze security alerts generated by network hardware and applications, enabling quicker responses to threats.
Incorporating intelligence gathered from recent cases involving the SesameOp backdoor can further enhance defenses. Always stay updated on the latest findings within the industry; as seen in our exploration of AI and human editing, the intersection of technology and cyber threats is evolving rapidly.
Educating Employees: A Key Component of Cyber Defense
Employees remain the first line of defense against threats like the SesameOp backdoor. By providing thorough training and resources, organizations can equip their team members to recognize potential phishing attempts and other tactics used by cybercriminals. It is critical to foster a culture of security within the workplace by:
- Hosting Regular Training Sessions: Keep employees informed about the latest threats and safe browsing practices.
- Encouraging Open Communication: Promote a workplace environment where employees feel comfortable reporting suspicious activities without fear of reprisal.
These initiatives are imperative, as highlighted in our assessment of parenting concerns in the digital age. Cybersecurity is a shared responsibility, and fostering collaboration between technology and human awareness is essential.
Future Trends: Preparing for Evolving Threats
As we look towards the future, it’s evident that threats like the SesameOp backdoor will continue to evolve. Organizations must stay ahead of these trends through constant research and development. The anticipated surge in AI adoption, as discussed in our analysis of new legislation affecting the job market, means that cyber defenses must also advance in sophistication and technique.
Implementing innovative cybersecurity solutions, similar to strategies discussed in our feature on AI marketing initiatives, can provide businesses with the edge they need to protect their assets efficiently.
To deepen this topic, check our detailed analyses on Cybersecurity section.