Cybersecurity is becoming more crucial than ever, especially with constantly evolving threats like the ZeroDayRAT spyware. This new mobile spyware platform has raised alarms among cybersecurity researchers due to its capabilities for real-time surveillance and data theft. Shockingly, the spyware is being actively advertised on platforms like Telegram, simplifying access for malicious actors. According to a recent report, this sophisticated malware can infiltrate both Android and iOS devices, making it one of the most dangerous threats in today’s digital landscape. As we dive deeper into this issue, we’ll uncover how ZeroDayRAT spyware works, its implications for users, and how it compares to traditional threats.
Understanding the ZeroDayRAT Spyware Threat
The ZeroDayRAT spyware is designed to exploit vulnerabilities in mobile devices, enabling attackers to conduct real-time surveillance with alarming ease. Cybersecurity experts like Daniel Kelley from iVerify note that the platform offers a complete suite of capabilities, making it more than just typical data-collection malware. Once established on a victim’s device, this malware allows an operator to access critical information such as model, location, operating system, and even app usage, transforming it into a comprehensive surveillance tool.
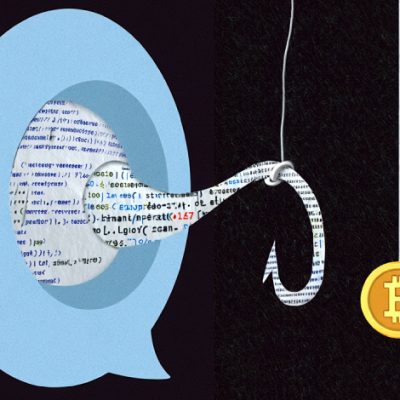
Moreover, the installation of this spyware often leverages social engineering tactics or fake app marketplaces, targeting unsuspecting users. The ability of ZeroDayRAT to monitor app notifications and recent SMS messages places it in a league of its own, as it creates detailed profiles of victims. This capability opens the door to various nefarious activities, including potential financial theft and invasion of privacy.
Key Features of ZeroDayRAT Spyware
The ZeroDayRAT spyware boasts several alarming features that make it a formidable opponent in the realm of mobile security. Some of the core functionalities include:
- Keystroke Logging: The spyware can capture keystrokes, effectively logging passwords and other sensitive data.
- Access to SMS Messages: It can retrieve SMS messages, including one-time passwords (OTPs), to bypass two-factor authentication.
- Real-Time Surveillance: The spyware can activate a device’s camera and microphone, allowing the attacker to monitor the victim remotely.
- Financial Theft: A specialized stealer component is embedded to target cryptocurrency wallet apps, rerouting funds to an attacker-controlled account.
These features make ZeroDayRAT an all-encompassing toolkit for mobile compromise, providing attackers with everything they need to infiltrate a victim’s life completely. The implications of such capabilities are extensive and alarming for users, particularly when considering the pervasiveness of mobile device usage in daily life.
Evolution and Methods of Distribution
The evolving tactics of mobile malware, including ZeroDayRAT spyware, reflect the continuous battle between cybersecurity measures and malicious actors. Researchers have observed that similar malware is often distributed through social engineering tactics or exploiting official apps. For instance, an Android RAT called Arsink has been found using reputable platforms like Google Apps Script for various nefarious activities, showcasing how even trusted brands can be leveraged to spread malware.
Additionally, security vulnerabilities within popular platforms can create opportunities for malware like ZeroDayRAT to proliferate. Recent campaigns that have surfaced illustrate how attackers use techniques such as phishing and masquerading as popular applications to trick users into installation. This technique resembles the strategies discussed in our analysis of Clayrat spyware, emphasizing the persistent risk posed to users.
Recent Incidents and Case Studies
Several noteworthy incidents highlight the aggressive nature of mobile malware, including ZeroDayRAT spyware. For example, a malicious app, All Document Reader, attracted over 50,000 downloads before being flagged for distributing a banking trojan. This incident underscores the potential dangers associated with downloading apps from unofficial sources.
Research indicates that the malware landscape is incredibly dynamic, with new threats emerging routinely. An Android banking trojan called deVixor has recently targeted users in specific regions through deceptive websites, showcasing how attackers localize their efforts for maximum impact. Given this context, understanding how ZeroDayRAT operates can help users protect themselves against similar intrusions. For an in-depth exploration of related mobile threats, consider reviewing our coverage of an emerging pixnapping vulnerability.
Protecting Yourself from ZeroDayRAT Spyware
Safeguarding against ZeroDayRAT spyware requires a multi-faceted approach to mobile security. Here are some essential practices:
- Be Cautious with App Downloads: Only download apps from verified sources such as the Google Play Store or official app stores.
- Utilize Strong Security Measures: Employ comprehensive security solutions that can detect malware and prevent unauthorized access.
- Stay Informed: Keep up with the latest cybersecurity news and updates to remain aware of emerging threats, similar to insights provided in our device reviews section.
By adhering to these guidelines, users can mitigate the risks posed by mobile spyware like ZeroDayRAT and ensure their digital safety.
Conclusion: The Ongoing Threat of ZeroDayRAT Spyware
As the capabilities of spyware like ZeroDayRAT continue to expand, so too does the need for vigilance among mobile users. The combination of sophisticated features, aggressive distribution methods, and the ability to conduct real-time surveillance makes it an unprecedented threat. Understanding this malware’s insidious nature can empower individuals to take proactive measures in protecting their privacy and financial security.
To deepen this topic, check our detailed analyses on Artificial Intelligence section.