In an age defined by rapid technological advancements and pervasive information overload, the old adage “trust but verify” takes on a new urgency. When it comes to cybersecurity, merely granting trust without ongoing verification is a recipe for disaster. Surprisingly, many organizations operate under an implicit trust model, especially with software-as-a-service (SaaS) platforms. Once a user or application is granted access, that trust remains unchecked, creating vulnerabilities that can be easily exploited. This article explores the disconnect between trust and the verification process, highlighting the necessity of continuous scrutiny in today’s digital landscape.
Understanding Implicit Trust in SaaS
In the world of SaaS, each integration or API token represents a relationship based on implicit trust. When a user clicks “Allow” to grant an app access, that application is treated as a trusted ally within your organization. However, this approach often leads to significant security gaps. For example, OAuth tokens can remain valid for extended periods, sometimes even indefinitely if not actively revoked.
This lack of re-evaluation poses a risk. Consider a marketing app that was authorized last year; if it has been granted unrestricted access, it still holds the keys to your data, even if no one is utilizing it today. Additionally, permissions granted often exceed what’s necessary. Users might allow an app to edit or delete when it only requires read access. This overreach can create an open door for potential breaches.
The Zero Trust Gap: Verifying Once
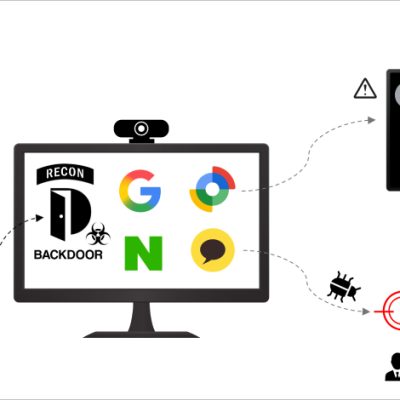
Ironically, while many organizations embrace the Zero Trust philosophy—believing in “never trust, always verify”—the reality is often quite different. Once access is granted through an initial OAuth authorization screen, verification typically ceases. The application retains persistent access, and there are no mechanisms in place for ongoing checks on the token’s legitimacy. As a result, the trusting relationship between the application and your systems continues unchecked.
This flaw becomes clear when we consider security measures like Single Sign-On (SSO) and Multi-Factor Authentication (MFA), which protect the entry points for user logins. Still, API tokens operate independently of these safeguards. With automation, it is easy to overlook what these tokens can do. They grant broad access without evaluating their usage repeatedly.
Identifying Blind Spots in Security
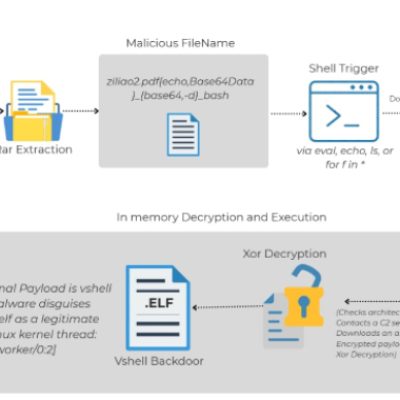
This landscape of unmonitored tokens creates glaring blind spots in security. Traditional security teams effectively monitor user logins and endpoint activities, but SaaS tokens often go unnoticed. Numerous incidents have demonstrated the fallout from this oversight. For example, in early 2023, a breach occurred when cybercriminals stole employee tokens from Slack, allowing them to access internal code repositories without needing password authentication.
Another significant breach involved CircleCI, where malware on an engineer’s laptop captured a session token, granting unauthorized access to sensitive information. As we advance to 2025, breaches have become even bolder. The Salesloft/Drift incident exemplifies this; hackers stole OAuth tokens meant for Salesforce integration, effectively turning them into master keys to sensitive data. These incidents underscore the urgent need for continuous verification and monitoring of app behavior.
Continuous Verification: A Paradigm Shift
In a true Zero Trust model, access should be assessed continuously, rather than at a single checkpoint. Continuous verification delves deeper into understanding the distinction between observed privilege and granted privilege. Granted privilege reflects the access initially provided, while observed privilege tracks how that access is utilized. For instance, if an API key typically reads ten records daily between 9 a.m. and 5 p.m., any drastic deviation—like an attempt to export the entire database at 2 a.m.—should be flagged for immediate investigation.
According to Gartner’s CARTA (Continuous Adaptive Risk and Trust Assessment) model, this ongoing scrutiny should become a standard practice. By continuously earning and re-earning trust based on real behavior, organizations can better safeguard their systems from potential intrusions.
Conclusion: Trust, But Continuously Verify
The crux of the issue with “trust but verify” is not that the principle itself is flawed, but rather that it is often ignored after the initial trust is established. To address the growing security gap, it is essential to foster a culture of continuous questioning regarding access: Is this behavior normal? Does this use of privilege still make sense? Only by adopting this mindset can organizations transform the concept of Zero Trust from a mere motto into a solid operational policy.
To enhance security protocols, companies can leverage solutions that continuously analyze privileges against observed behavior, highlighting misused tokens and over-privileged applications. This proactive approach facilitates real-time verification where it has historically been lacking. If you want to learn more about enhancing your cybersecurity posture and bridging this critical gap, check out these insightful articles: why we need a trust-boosting revolution and why verifying information matters now more than ever.
To deepen this topic, check our detailed analyses on Cybersecurity section.