In the ever-evolving landscape of cybersecurity, vulnerabilities in systems can lead to shocking revelations. Recently, a serious threat has emerged from the Red Hat OpenShift AI vulnerability, which potentially allows attackers to gain complete control over hybrid cloud infrastructures. This vulnerability, tracked as CVE-2025-10725, has a CVSS score of 9.9, highlighting its severity. The implications are alarming: an authenticated low-privilege user could gain full administrative privileges, jeopardizing the integrity and availability of sensitive data. Understanding and addressing this flaw is crucial for organizations that rely on the OpenShift platform.
Understanding the Red Hat OpenShift AI Vulnerability
The Red Hat OpenShift AI vulnerability primarily stems from an overly permissive ClusterRole, enabling low-privileged users to escalate their privileges. An authenticated user, such as a data scientist utilizing a standard Jupyter notebook, can exploit this flaw to become a cluster administrator. This capability allows the attacker to disrupt services and potentially steal sensitive information, compromising the security of the entire cluster and all its hosted applications. The significance of this vulnerability cannot be overstated, as it impacts versions 2.16, 2.19, 2.21, and 2.22 of the platform.
Real-World Implications of the Vulnerability
The recent disclosure of the Red Hat OpenShift AI vulnerability raises questions regarding the robustness of hybrid cloud infrastructures. For instance, imagine an organization that relies heavily on OpenShift for deploying machine learning models across its operations. If a malicious actor gained access through this vulnerability, they could steal confidential data or cause significant disruptions. An attacker might leverage a scheduled job in a privileged namespace to exfiltrate critical ServiceAccount tokens, escalating their access progressively until they achieve root control on cluster master nodes. Such an event can lead to total compromise and raise alarm bells across the cybersecurity landscape.
Preventative Measures for Organizations
Given the severity of the Red Hat OpenShift AI vulnerability, organizations using affected versions must take swift action. Red Hat initially recommended avoiding broad permissions and revoking the ClusterRoleBinding associated with the kueue-batch-user-role. However, following updates, additional steps have been outlined. For RHOAI versions 2.19 and above, administrators can:
- Set the Kueue component management state to “Removed” if certain features are unnecessary.
- Apply annotations to prevent the RHOAI operator from managing the kueue-batch-user-rolebinding.
- Disable the ClusterRoleBinding by updating its subject to a non-existent group.
Such precautions are vital to mitigating risks and ensuring organizational security amidst increasingly sophisticated cyber threats.
Recent Trends in Cybersecurity and Vulnerabilities
The announcement of the Red Hat OpenShift AI vulnerability coincides with a wave of other concerning revelations in the cybersecurity domain. For example, researchers uncovered AI flaws in Google Gemini, leading to vulnerabilities in prompt injections that could also be exploited similarly. Additionally, a recent rootkit patch was released to combat escalating threats amid federal breaches, highlighting the ongoing battle against cybersecurity threats.
Understanding these vulnerabilities helps organizations appreciate the importance of proactive measures. As explored in our analysis of the Google Gemini AI flaws, awareness and education systems play a crucial role in combating these issues.
Conclusion: Ensuring Security in Hybrid Cloud Environments
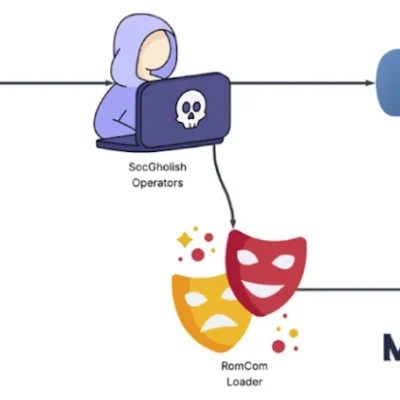
The Red Hat OpenShift AI vulnerability serves as a stark reminder of the challenges faced by organizations utilizing hybrid infrastructures. It emphasizes the critical need for security measures and constant vigilance. As solutions like OpenShift continue to evolve, so too must the strategies for protecting sensitive data and ensuring the overall integrity of systems. Organizations are encouraged to keep their systems updated and monitor for emerging threats, similar to strategies discussed in our coverage of rootkit security enhancements and the tactics employed by hacker groups as outlined in our report on the Phantom Taurus hacker group.
To deepen this topic, check our detailed analyses on Cybersecurity section