In the world of cybersecurity, new threats emerge daily, causing substantial risks to individuals and organizations alike. One such significant threat is Konni malware, a remote access Trojan (RAT) that has been increasingly used in sophisticated cyberattack campaigns. With shocking statistics indicating a rise in malware-related incidents, understanding this particular strain has become essential for anyone concerned about their digital safety. This article delves into the specifics of Konni malware, its deployment methods, and its far-reaching implications, offering a comprehensive overview for those looking to protect themselves in an ever-evolving tech landscape.
Understanding Konni Malware: How It Operates
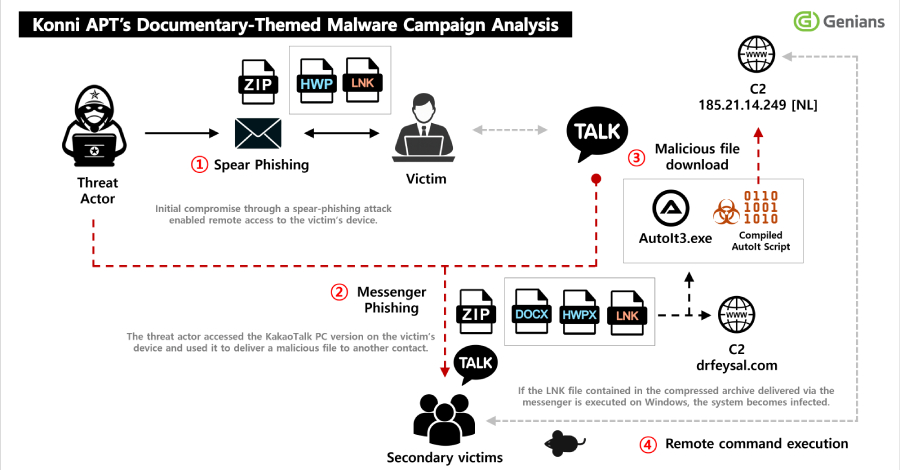
Konni malware operates primarily through spear-phishing tactics, targeting unsuspecting victims to gain unauthorized access to their systems. Recent research highlights that North Korean threat actors are behind these attacks, employing a multi-faceted approach to infiltrate networks. Initially, victims receive an email disguised as a legitimate communication—often purporting to relate to human rights issues in North Korea. Upon opening a malicious attachment, such as a Windows shortcut (LNK file), the malware is executed, enabling the threat actors to establish control over the victim’s system.
The effectiveness of Konni malware lies in its ability to remain hidden while it collects sensitive information over an extended period. Victims may unknowingly have their internal documents compromised as the malware silently siphons off data. Moreover, the malicious actors exploit the compromised systems further by using KakaoTalk, a popular messaging application, to disseminate the malware to other contacts within the victim’s network. This method smartly utilizes the trust existing within personal and professional relationships to lure in additional targets.
The Phishing Technique Behind Konni Malware
The utilization of spear-phishing emails is a hallmark of Konni malware. The process generally begins with a carefully crafted email that tricks the recipient into believing they are receiving important information. The message may contain references to North Korean affairs, making it all the more compelling for specific audiences.
- Upon clicking on the ZIP file attachment, victims inadvertently execute the malware.
- As the malware installs itself, it begins a process of information theft and network infiltration.
Additionally, Genians Security Center documents one instance where the malware allowed the attackers to send malicious ZIP files via the victim’s KakaoTalk application. This strategy of using a trusted application makes it easier to spread malware, as recipients are more likely to open files from known contacts. The clever manipulation of social engineering elevates the effectiveness of this malware campaign.
Long-term Persistence and Impact of Konni Malware
One of the most alarming aspects of Konni malware is its long-term persistence on infected systems. Once this malware is inside a network, it can remain undetected for extended periods, posing significant risks to organizations. The capability to gather internal documents while maintaining a low profile complicates detection efforts and remediation strategies.
- This extended access enables attackers to meticulously plan further infiltration strategies.
- Organizations may find themselves addressing breaches months after the initial compromise.
Moreover, the use of various RAT families amplifies the malware’s resilience. Competent adversaries may deploy multiple RATs on a single victim’s machine to ensure persistence and effectiveness. The sophisticated nature of the attack ultimately raises significant challenges for cybersecurity professionals.
Defensive Measures Against Konni Malware
Preventing the infiltration of Konni malware and similar threats requires an ongoing commitment to cybersecurity best practices. Here are key strategies that organizations and individuals can implement:
- Educate employees about phishing techniques and the dangers of unsolicited attachments.
- Implement robust email filtering solutions to detect and block suspicious messages.
- Regularly update software and systems to close vulnerabilities that may be exploited by malware.
- Utilize intrusion detection systems (IDS) to monitor for unusual activity on networks.
By putting these measures in place, organizations can significantly reduce their risk of becoming victims of Konni malware and similar threats.
Conclusion: Staying Ahead of Konni Malware Threats
The threat posed by Konni malware underscores the evolving landscape of cyber threats we face today. With its dual approach that combines spear-phishing and social engineering tactics, the malware emphasizes the critical need for heightened vigilance and robust security measures. As explored in our analysis of Jewelbug, a similar cyber threat, organizations must remain abreast of emerging risks. By adopting a proactive stance toward cybersecurity, we can better protect our sensitive information and systems from the clutches of malicious actors.
To deepen this topic, check our detailed analyses on Artificial Intelligence section