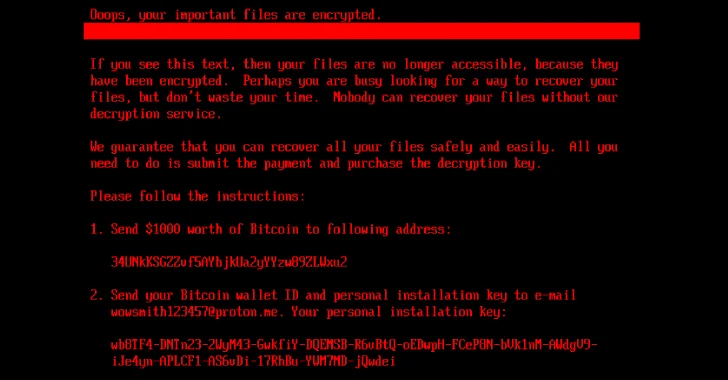
In the ever-evolving landscape of cybersecurity, the emergence of HybridPetya Ransomware marks a concerning trend in malware evolution. This ransomware variant uniquely exploits vulnerabilities, particularly the recently identified CVE-2024-7344, to bypass UEFI Secure Boot. The ramifications are significant: it compromises systems by circumventing one of the most critical security features designed to protect against unauthorized firmware modifications. Recent data indicates that organizations using outdated firmware are three times more likely to experience a ransomware attack in 2025. As businesses escalate their digital transformation, understanding the implications of such threats becomes paramount.
HybridPetya Ransomware Exposure and Exploits
HybridPetya Ransomware operates through sophisticated mechanisms that allow it to exploit existing vulnerabilities effectively. One notable aspect is its ability to leverage CVE-2024-7344. This particular vulnerability enables an attacker to alter boot processes, hence evading standard security measures such as Secure Boot. Organizations are urged to update their firmware regularly to mitigate such risks. Studies have shown that nearly 70% of corporate systems lack the latest firmware updates that could prevent such intrusions. For more information on this critical issue, view the report on Microsoft’s security updates.
Best Practices to Mitigate HybridPetya Risks
To effectively mitigate the risks associated with HybridPetya Ransomware, organizations should adopt several proactive measures. Firstly, implementing regular system updates is crucial. This includes not only operating systems but also firmware and security software. Companies should conduct vulnerability assessments to identify and rectify weaknesses in their IT infrastructure. Moreover, adopting a multi-layered security approach can significantly decrease the chances of infection. For businesses looking to enhance their digital resilience, emerging tools and technologies can be pivotal. Learn how AI-driven tools are transforming security landscapes.
📊 Key Recommendations
- Maintain Updated Firmware: Regular updates can thwart ransomware attacks.
- Conduct Regular Security Audits: Identify vulnerabilities before they can be exploited.
Understanding the Broader Implications of HybridPetya
As the HybridPetya Ransomware continues to evolve, it presents severe implications not only for individual organizations but for the cybersecurity landscape at large. The convergence of malware sophistication and the complacency of updates can lead to catastrophic data breaches. Companies must remember that the cost of prevention is significantly lower than the impact of a successful attack. The statistics are alarming; businesses that endure a ransomware attack can expect losses between $500,000 to over $5 million, including recovery efforts, downtime, and lost revenue. For more insights on threats affecting various industries, check out relevant discussions surrounding diverse technological initiatives.
Key Takeaways and Final Thoughts
In summary, the rise of HybridPetya Ransomware underscores the critical need for businesses to prioritize cybersecurity. Regular updates, proactive risk assessments, and a robust response strategy are vital for protection. As the frequency and sophistication of such attacks increase, staying informed, as well as implementing stringent security measures, can significantly improve organizational resilience against evolving threats.
❓ Frequently Asked Questions
What can organizations do to prevent HybridPetya?
Organizations should implement regular firmware updates and conduct vulnerability assessments to detect weaknesses in their security. Additionally, employing multi-layered security strategies can also be effective.
How does HybridPetya compromise systems?
HybridPetya exploits vulnerabilities, particularly CVE-2024-7344, by manipulating boot processes and bypassing essential security features, enabling it to execute malicious actions on compromised systems.
To deepen this topic, check our detailed analyses on Cybersecurity section