In an era where cyber threats rapidly evolve, the risk grows significantly with seemingly innocuous tools like add-ins. Recent events have highlighted how an Outlook Add-Ins Hijack can turn trusted applications into gateways for malicious activities. A shocking statistic reveals that more than 4,000 Microsoft account credentials were compromised through a single compromised add-in. This alarming incident exemplifies the vulnerabilities within tools we often take for granted. The intention behind this article is to enlighten users on the perils of overlooked software components and to stress the importance of rigorous security practices.
Understanding the Scope of **Outlook Add-Ins Hijack**
The manipulation of productive applications, particularly Outlook, showcases how cybercriminals exploit common software functionalities. The hijacking of the legitimate AgreeTo add-in transformed it into a phishing kit, illustrating a significant vulnerability in the software supply chain. During this incident, attackers gained control over a domain linked to a now-abandoned project, deploying a counterfeit Microsoft login page that users readily trusted.
- The compromised add-in had a direct impact on user trust, as it operated within the familiar Outlook environment where sensitive communications occur.
- This incident underlines how simple add-ins can request permissions that threaten user safety by accessing and modifying critical email content.
As highlighted by Koi Security’s Idan Dardikman, these add-ins dwell in a space where “implicit trust” is often assigned based solely on their origin from Microsoft’s own store, revealing the oversight in protecting against such threats.
What Makes **Add-Ins** a Target for Attackers?
**Outlook Add-Ins Hijack** incidents exemplify several strategic attack vectors commonly leveraged by threat actors:
- Permissiveness: Add-ins can gain elevated privileges to manipulate emails, making them an enticing target for attackers looking to gather sensitive data.
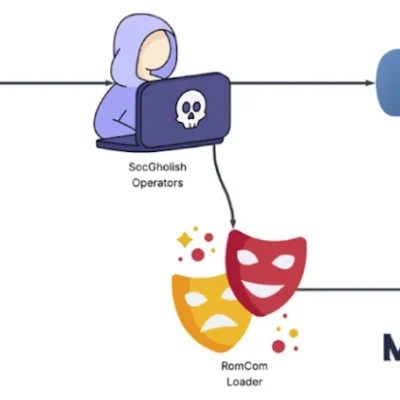
- Legacy Technologies: Cybercriminals often combine outdated techniques with modern tools. This dual approach can exploit unaware users by slipping through traditional security measures.
The reliance on established workflows inadvertently creates entry points for attackers. Cloud services and trusted applications become hunting grounds when attackers find weak points in their defenses.
Recent Trends Tied to **Outlook Add-Ins Hijack**
Beyond the immediate risks posed by hijacked add-ins, there’s a broader trend of using well-known platforms as vectors for more extensive attacks. Google recently addressed a high-severity zero-day flaw in Chrome (CVE-2026-2441), demonstrating how swiftly attackers can capitalize on vulnerabilities through various technologies, including browser exploits and cloud abuse. The ongoing evolution of threats, such as breaches through BeyondTrust vulnerabilities, reinforces the need for organizations to reconsider and tighten their cybersecurity strategies.
- The recent discoveries show cyber actors utilizing AI to automate vulnerability exploitation, which can increase the speed at which attacks occur.
- Exposure of legacy systems remains a concern, as malicious actors continue to leverage established infrastructure for their operations.
As cybersecurity practices develop, constant monitoring and adapting to new threats become paramount in safeguarding organizational information.
The Implications of Ignoring **Outlook Add-Ins Security**
Neglecting the security of Outlook add-ins can lead to widespread repercussions:
- Data Breaches: As seen during the phishing incident, attackers can acquire a trove of credentials leading to significant data losses.
- Trust Erosion: If users become aware of repeated security failures, their trust in the software ecosystem declines, impacting user engagement and adoption rates.
To combat these threats, companies should prioritize robust security practices, including regular audits, training for employees on recognizing phishing attempts, and ensuring software is always up to date with the latest patches.
Conclusion: Securing Against **Outlook Add-Ins Hijack**
Incidents of Outlook Add-Ins Hijack serve as a clarion call for vigilance in cybersecurity practices. The malicious exploitation of widely used software can result in severe consequences, including data breaches and erosion of trust. Organizations must adopt a proactive stance, integrating advanced threat detection and response systems while remaining vigilant against evolving attack methods. By emphasizing education and regularly reviewing security protocols, companies can mitigate the risks posed by seemingly harmless add-ins.
To deepen this topic, check our detailed analyses on Cybersecurity section.
Additionally, similar incidents such as the discovery of the WhatsApp worm and the Chaosbot malware expose the breadth of current vulnerabilities in popular platforms. Organizations must remain aware and responsive to cybersecurity challenges, especially as threats continue to arise.