In today’s rapidly evolving digital landscape, understanding the threats posed by cyber espionage is paramount. One such threat is the recently discovered NANOREMOTE Malware, a sophisticated backdoor that utilizes the Google Drive API for remote control over Windows systems. According to cyber security researchers at Elastic Security Labs, this malware exhibits alarming characteristics, allowing for seamless data theft and control, evading detection efficiently. The implications of its capabilities raise significant concerns for individuals and organizations alike, especially given the substantial increase in cyber attacks in recent years. In this article, we will explore the functionalities, origins, and potential impacts of NANOREMOTE Malware, providing valuable insight into this emerging threat.
Unveiling the Capabilities of NANOREMOTE Malware
The NANOREMOTE Malware operates primarily as a Windows backdoor, empowering cyber attackers to exploit victims’ systems extensively. This malware facilitates a unique command-and-control (C2) system through the Google Drive API, creating a channel for data exfiltration and other malicious activities. According to Daniel Stepanic, a principal security researcher at Elastic Security Labs, one of its standout features includes the ability to ship data to and from infected endpoints using Google Drive as a relay.
This innovative method makes it difficult for traditional security measures to detect the ongoing attacks. The malware’s task management system allows the operators to manage file transfers efficiently, which includes abilities to queue, pause, resume, and cancel file transfers. This capability enhances the stealthiness of NANOREMOTE Malware, making it a substantial threat to various sectors.
The Rise of the REF7707 Threat Cluster
The NANOREMOTE Malware is believed to be associated with the REF7707 threat cluster, suspected to be linked to Chinese cyber operations. This group has a history of targeting critical sectors, including government and telecommunications, particularly in Southeast Asia and South America. The sophisticated nature of the malware indicates a well-organized cyber espionage campaign, as explored in our analysis of exploits in remote access vulnerabilities.
Interestingly, the malware shows code similarities with an existing implant codenamed FINALDRAFT, known for utilizing Microsoft Graph API for its C2 operations. Security analysts at Palo Alto Networks Unit 42 have tracked this cluster’s activities back to early 2023, providing substantial evidence of ongoing cyber threats posed by REF7707.
Technical Insights into NANOREMOTE Malware
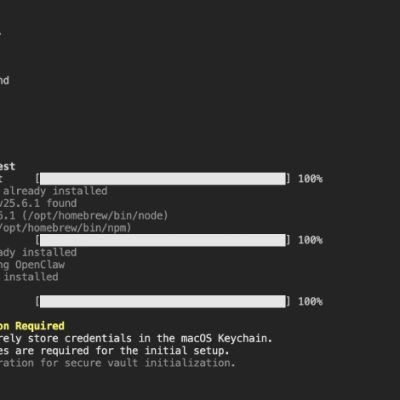
Analyzing the technical architecture of NANOREMOTE Malware reveals a robust framework designed for various malicious operations. Written in C++, this malware is crafted to perform reconnaissance, execute commands, and manage files across compromised environments using the Google Drive API as an intermediary. Its initial access method remains speculative, but it operates through a loader named WMLOADER that mimics a legitimate component.
Once deployed, the malware communicates with hard-coded, non-routable IP addresses over HTTP, processing commands sent by the attacker through compressed JSON data transmitted via POST requests. Remarkably, the data is encrypted with a 16-byte AES-CBC key (558bec83ec40535657833d7440001c00), showcasing an advanced level of sophistication in its operation.
Examples of Cyber Exploits Featuring Malware Similarities
The infrastructure of NANOREMOTE Malware echoes some tactics seen in other recent cyber threats, such as the ChaosBot malware, which also employs social engineering techniques to hijack communications. Another relevant incident is the exploitation of Discord for control, illustrating the adaptive nature of malware distribution. Such comparisons highlight the evolving strategies utilized by cybercriminals.
- Advanced task management through Google Drive operations.
- Use of encrypted communications to avoid detection.
Consequences for Victims and Protective Measures
Organizations targeted by NANOREMOTE Malware face severe risks, including data theft and operational disruption. The malware’s stealth-based operations complicate the identification of breaches, making it imperative for organizations to enhance their security protocols. Continuous monitoring and adopting advanced threat detection measures are pivotal in defending against such sophisticated cyber threats.
As highlighted in a recent analysis of cybersecurity trends, organizations must remain vigilant and implement robust security training, using insights from our detailed overview of weekly cybersecurity threats.
Conclusion: Staying Ahead of Cyber Threats
In conclusion, the emergence of NANOREMOTE Malware serves as a stark reminder of the evolving landscape of cyber threats. As cybercriminals develop innovative methods to exploit systems, awareness and proactive measures become essential for individuals and organizations alike. To further safeguard against these threats, organizations can refer to several studies and reports. One such report examines the vulnerabilities present in systems that can lead to significant data exposure, analogous to the concerns raised by recent software package exploitations. Protecting sensitive information must remain a top priority in this digital age.
To deepen this topic, check our detailed analyses on Cybersecurity section